When your security team, legal counsel, or procurement committee vets a new SaaS vendor, one question comes up early: is this platform SOC 2 compliant? For organizations subject to GDPR, CCPA, or internal data governance policies, using a consent management platform that hasn't been independently audited isn't an option — the risk to your customer data and your compliance posture is simply too high.
Many consent management tools make broad claims about security without the independent verification to back them up. Chasing down vague "we take security seriously" answers from vendor support teams — or worse, trying to interpret self-certified security pages — wastes your team's time and leaves real questions unanswered.
Secure Privacy takes a different approach. As a SOC 2 compliant consent management platform, Secure Privacy undergoes rigorous, independent third-party audits that verify its security, availability, and confidentiality controls against the AICPA's recognized Trust Service Criteria. Your due diligence process has a clear, audited answer.
By the end of this article you'll know exactly what Secure Privacy's SOC 2 compliance covers, what it means for your organization's data, and the precise steps to request the full audit report for your vendor review.
Who Is This Article For?
This article is for current and prospective Secure Privacy customers who need formal confirmation of Secure Privacy's security posture — including:
Security engineers and InfoSec teams conducting vendor risk assessments
Compliance officers evaluating consent management platforms against GDPR, CCPA, or ISO requirements
Legal teams and procurement stakeholders reviewing SaaS vendor due diligence documentation
Anyone asking: "Is Secure Privacy SOC 2 certified, and how do I get the report?"
What Is SOC 2 Compliance?
SOC 2 is an auditing standard developed by the American Institute of Certified Public Accountants (AICPA). It evaluates how service organizations manage and protect customer data based on five Trust Service Criteria:
Security — protection against unauthorized access
Availability — systems are operational and accessible as committed
Processing Integrity — processing is complete, accurate, and authorized
Confidentiality — designated confidential information is protected
Privacy — personal information is collected, used, and disclosed appropriately
Achieving SOC 2 compliance demonstrates that a company has effective, independently audited controls in place to protect sensitive customer data on an ongoing basis — not just a self-assessment, but a verified third-party opinion.
Secure Privacy SOC 2 Compliance Status
Secure Privacy is SOC 2 compliant and undergoes independent third-party audits to validate its security and operational controls. You can review Secure Privacy's full compliance posture on the official compliance page:
Secure Privacy Compliance Overview — compliance.secureprivacy.ai
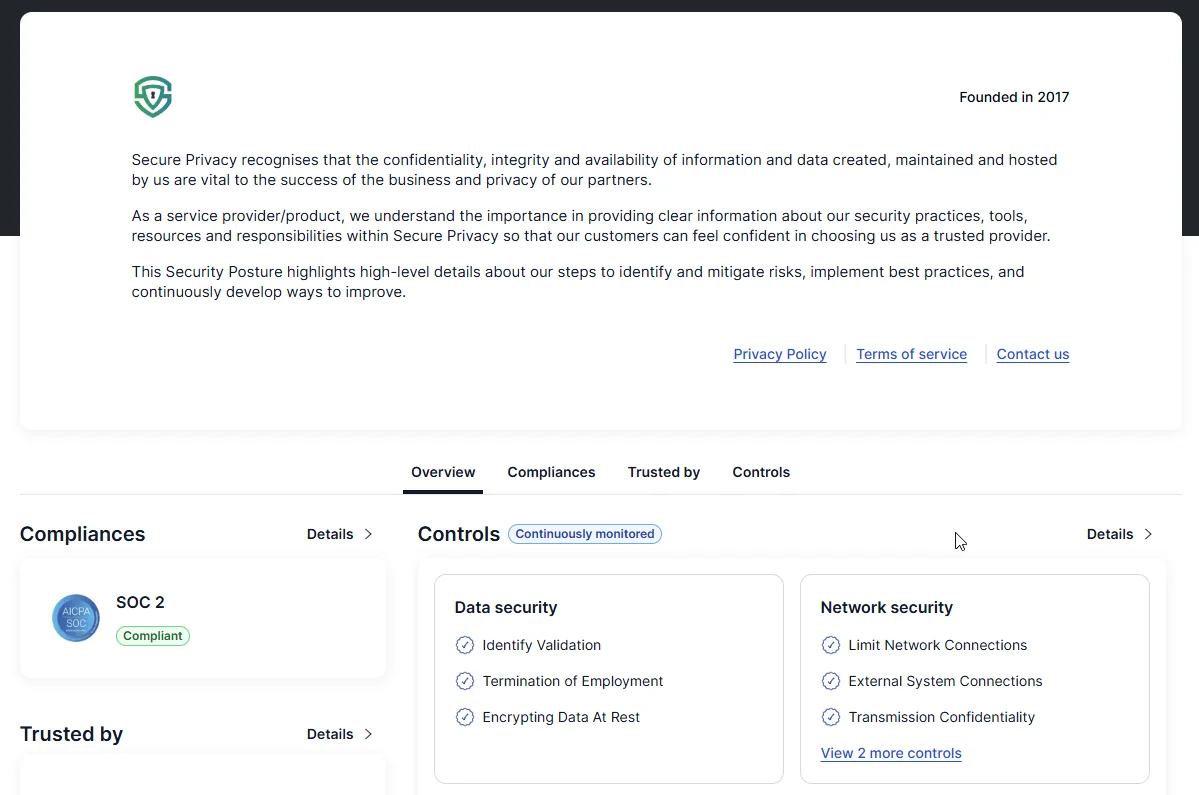
Secure Privacy's compliance dashboard at compliance.secureprivacy.ai showing current SOC 2 status.
What SOC 2 Compliance Means for Your Organization
When you deploy Secure Privacy as your consent management platform, SOC 2 compliance gives your organization concrete assurances:
Your customer data is protected by independently verified security controls — not self-reported ones
Secure Privacy's systems are monitored and maintained for high availability, reducing risk of service disruption affecting your consent records
Internal processes follow recognized industry security best practices, aligned with AICPA standards
Formal risk management and incident response procedures are in place and audited
For organizations that must demonstrate third-party vendor due diligence under GDPR Article 28 (processor agreements) or similar frameworks, Secure Privacy's SOC 2 report is a critical piece of your compliance documentation.
How to Request the Secure Privacy SOC 2 Report
The full SOC 2 audit report is available to customers and prospective customers upon request. For security and confidentiality reasons, a signed NDA is required before the report can be shared. The process takes as little as two business days.
Step 1 — Contact the Secure Privacy Support Team
Email [email protected] to initiate your SOC 2 report request. Include your organization name and the context for your request (e.g. vendor assessment, procurement review) to help the team process it efficiently.
Step 2 — Review and Sign the NDA
The Secure Privacy team will provide a Non-Disclosure Agreement (NDA) for your review. Once your organization has reviewed and executed the NDA, your request moves to processing.
Step 3 — Receive the SOC 2 Report
After the NDA is executed, allow up to two business days for your request to be processed and the report delivered. Timing may vary slightly depending on the nature and scope of the request.
Frequently Asked Questions About Secure Privacy's SOC 2 Compliance
Is Secure Privacy SOC 2 certified?
Yes. Secure Privacy is SOC 2 compliant and undergoes independent third-party audits to validate its security, availability, and confidentiality controls. You can verify the current compliance status at compliance.secureprivacy.ai.
Can I download the SOC 2 report directly from the Secure Privacy website?
No. For security and confidentiality reasons, the SOC 2 report is not publicly available for direct download. A signed NDA is required before the report can be shared with your organization. Contact [email protected] to begin the process.
Which SOC 2 report type does Secure Privacy hold — Type I or Type II?
Details about the SOC 2 report type and audit scope are disclosed after an NDA is signed. Please contact [email protected] for specifics.
How long does it take to receive the SOC 2 report after requesting it?
After the NDA is signed, the SOC 2 report is typically delivered within two business days. Timing may vary slightly depending on the nature of the request and the internal review process.
Does Secure Privacy's SOC 2 compliance satisfy GDPR data processor requirements?
SOC 2 compliance is an important signal of a vendor's security maturity and is commonly used as supporting evidence in GDPR Article 28 vendor due diligence and data processing agreement reviews. For specific questions about how Secure Privacy's compliance posture aligns with your organization's legal requirements, we recommend consulting your Data Protection Officer and contacting [email protected] to request the full report.
Related Security & Compliance Articles
Secure Privacy GDPR Data Processing Agreement (DPA)[?]